Consumer group pushes for stricter EWA protections
Payments Dive
OCTOBER 16, 2023
In a recent web post, the National Consumer Law Center issued a number of policy recommendations for states seeking to regulate earned wage access companies.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 accessibility-policy
accessibility-policy 
Payments Dive
OCTOBER 16, 2023
In a recent web post, the National Consumer Law Center issued a number of policy recommendations for states seeking to regulate earned wage access companies.
Perficient
NOVEMBER 15, 2020
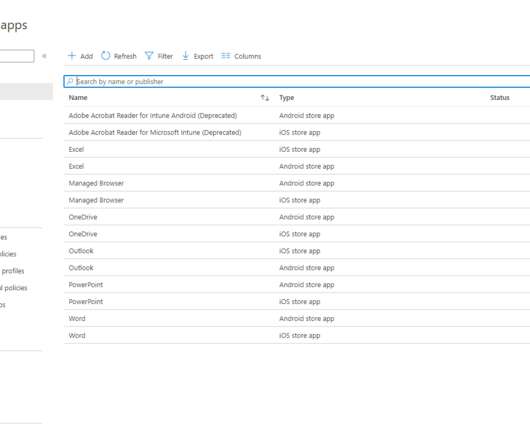
Securing the app (conditional access with MFA). With that said, let’s select the Add option so we can create a new app policy for Microsoft Teams. Now that the app policy has been created we’ll need to assign it to a group of users. Let’s start by creating a new Conditional Access policy.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Perficient
MARCH 23, 2021
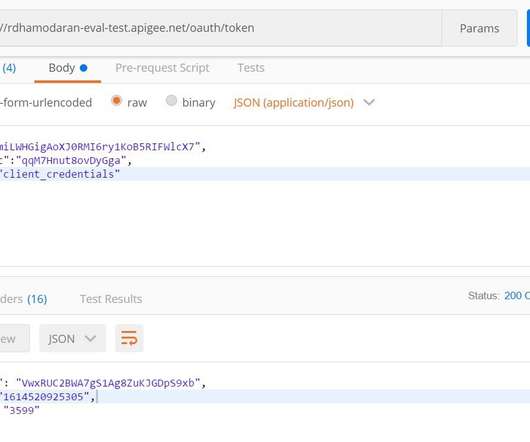
Client POST’s an API call to Apigee with client ID and client secret to fetch the access token from the registered developer application. Client application sends Json Request to Apigee edge to fetch access token. Create a OpenAPI specification to define the structure of grant type access token RESTful API. Sequence Diagram.
Perficient
MARCH 21, 2021
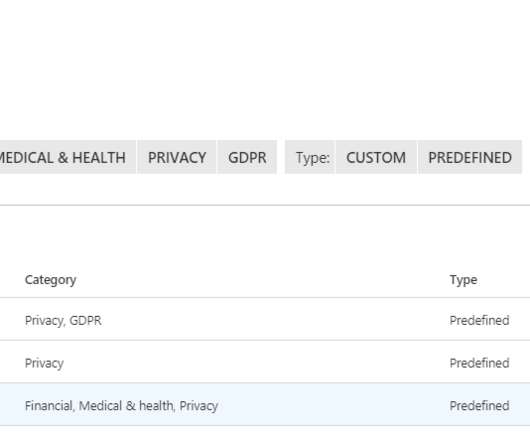
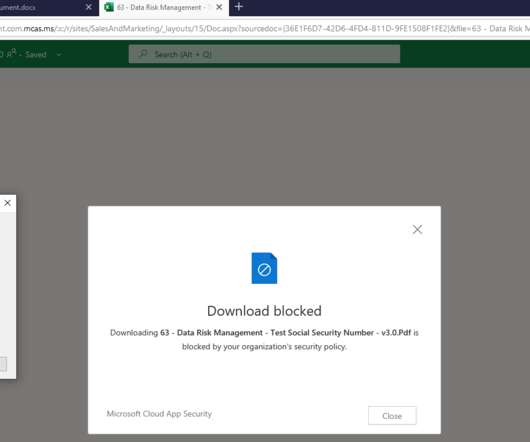
Where remote work has become the new norm, you will likely see many end-users using their own unmanaged devices to access corporate information. In today’s blog, I’ll show you how you can block downloading of files with sensitive data to unmanaged devices with the use of session policies in Microsoft Cloud App Security (MCAS).
Perficient
OCTOBER 3, 2020
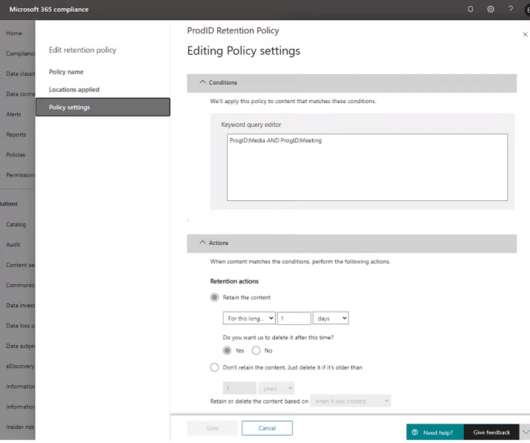
Starting this month (October 5th to be exact), you can enable your Teams meeting policy to have meeting recordings saved to OneDrive and SharePoint instead of Microsoft Stream! Retention policy application. Request access flow. No access, can request access (via request access flow). External/Guest users.
Perficient
MARCH 22, 2021
Last time we talked about controlling file downloads of sensitive content by using a session policy in MCAS. However, once we implemented the proper session policy in MCAS, we were able to look for files that contained sensitive information (in our case SSNs) and block anyone on an unmanaged device from downloading the file.

The Paypers
JUNE 7, 2021
The Bank of England has updated its website with a new Omnibus Accounts Access Policy.

Perficient
JULY 29, 2021
Once a needed data source is identified, it is best to have an automated approach to request requisite entitlements and a framework to access the information through various means—all while adhering to the firm’s data policy and security constructs.

Perficient
AUGUST 8, 2020
These sensitivity labels can also be associated with policies that handle privacy, external user membership, and even unmanaged device access. Policy Management Enhancements. Batch/Bulk Assignment of Policies now Generally Available. The PowerShell module supports: Policy assignment to O365 groups.

Perficient
FEBRUARY 1, 2021
Retain full control of your organization’s sensitive data that is accessed, stored, and transmitted to other parties with Oracle ERP Cloud. You can set the application security to align with your enterprise’s security policy. Establish and manage consistent encryption and key management policies.
Perficient
FEBRUARY 13, 2021
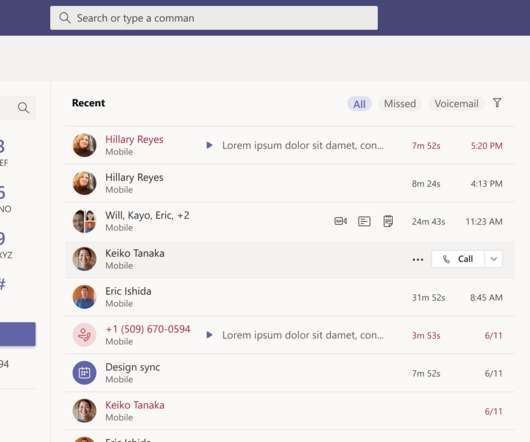
1:1 Call Recording Policy Introduction. Starting mid-March, Microsoft will begin changing how 1:1 Call recording is enabled by creating its own policy. Configuration Changes for Guess Access. For those of you with Guest Access disabled in your tenant, listen up! New Revised In-meeting Share Experience.

Perficient
JUNE 16, 2021
This metadata query facility should also facilitate the entitlement process by integrating with the firm’s workflow management tool to ensure full compliance with established data access policies. In my next post, I will share how Perficient can help enhance your data programs with our data lineage offerings.

American Banker
JANUARY 2, 2024
The Alabama-based bank loosened its funds availability policy in 2022 as part of an effort to give customers early access to their paychecks. "We We opened the door too wide, bad people came rushing in, and we didn't close the door timely enough," Regions' CFO said.

Perficient
JUNE 30, 2022
To ensure continued government support of the crypto and fintech sectors, the White Paper announced the establishment of the Digital Policy Council (DPC) headed by the Prime Minister, the Financial Secretary, the Executive Director of the SCB, the Governor of the Central Bank of The Bahamas, and the Chair of the Digital Advisory Panel.

Abrigo
MARCH 14, 2022
Accessibility of data for loan officers, managers and potentially external loan review personnel. Adequate loan administration software will allow an organization to access the hundreds of thousands of documents that some banks have on file. Access should be easy but not at the expense of data security.
Payments Source
MARCH 10, 2021
The Arizona Fintech Council, an organization of banks, economic and technology groups, will encourage collaboration and access to the state's regulatory sandbox to promote a version of Europe's open banking policy in the U.S.

Perficient
FEBRUARY 10, 2021
It is a mechanism by which the server will control access to its goodies, should that someone be running on a different domain. The browser sends some information via HTTP Access-Control-Request-* headers. The server makes a determination on headers received a sends back Access-Control-Allow-* headers. This is the heart of CORS.

PYMNTS
JANUARY 14, 2021
The Saudi Arabian Monetary Authority (SAMA) is introducing an open banking policy to advance digital innovation in the financial services sector. Through the initiatives in the policy, the goal is to foster the advancement of digital technologies and create new financial services and products.

Perficient
FEBRUARY 27, 2021
This certification all revolves around reducing risk by remediating active attacks, advising on improvements to threat protection practices, and referring violations of organizational policies to the appropriate parties. Certification – Microsoft Certified: Identity and Access Administrator Associate.

PYMNTS
SEPTEMBER 13, 2020
Europe's biggest banks have called on the European Commission to implement tough regulations for cryptocurrencies, such as stablecoins, that would protect consumers and preserve state sovereignty in monetary policy, Reuters reported. In a joint statement Friday (Sept. The association declined to comment, Reuters reported.

Perficient
NOVEMBER 2, 2020
This will give you more flexibility with how you want to present the whiteboard, and gives you the options of read-only mode, or allow others to edit and collaborate once given access. Incoming IP Video Policy Changes. You can learn more about this policy change here. Image provided by Microsoft. Chat and Collaboration Updates.

Perficient
MARCH 17, 2021
Restricted Access to Sensitive Information. It is important for regulators and clients to understand upfront who will have access to the most confidential data. It may not be necessary for each team member (depending on their role) to have access to this information to complete the project.

Perficient
FEBRUARY 15, 2024
Moving forward, it is advisable to: Risk Assessments: Conduct comprehensive risk assessments, comparing existing processes, policies, and standards to industry benchmarks while identifying emerging risks and potential gaps. Reporting: Have access to comprehensive reports showcasing ongoing compliance efforts.

Chris Skinner
APRIL 11, 2017
I blogged recently about American banks beating up the regulators to stop account access via APIs. Citi’s head of FinTech Policy, Andres Wolberg-Stok, got in touch to clarify the true situation. The only person who should access bank data is the customer, the banks bleat.” Well, they don’t.

Abrigo
FEBRUARY 16, 2024
Clearly defined policies and procedures can help avoid confusion and streamline credit operations. Assess and control key risk areas with an effective credit policy. Get details in "A guide to implementing credit policy." Discover options for loan policy review assistance. Prepare for your next exam.

American Banker
NOVEMBER 3, 2023
This week the Small Business Administration followed through with a controversial policy change by granting access to its flagship 7(a) program to three additional nonbank lenders. These new participants vowed to ramp up their small-business lending efforts.

Independent Banker
OCTOBER 1, 2022
Cyber insurance not only provides financial reimbursement for losses; it also equips the insured with access to a list of preapproved incident response experts that are required to help the bank manage a cyber event. Liability policies respond to lawsuits or any regulatory action and fines that result from a cyber event.

Perficient
FEBRUARY 15, 2024
We recommend that impacted organizations prioritize the following actions as part of a holistic approach to the regulation: Risk Assessments: Conduct comprehensive risk assessments, comparing existing processes, policies, and standards to industry benchmarks while identifying emerging risks and potential gaps.

TheGuardian
MAY 7, 2023
Exclusive: HSBC and NatWest staffers seconded to shadow business secretary Jonathan Reynolds’s team Labour has been criticised for giving global banks access to parliament after taking an HSBC staffer into its shadow business team, despite the financial giant coming under fire over its links with China.

PYMNTS
AUGUST 7, 2020
Microsoft and Facebook are grumbling publicly about fellow tech giant Apple ‘s policies restricting access to coveted slots in its App Store, as well as the access given to iPhone and iPad users. 15, Microsoft plans to release Project xCloud , a streaming service that will allow users to play any of roughly 100 games.

PYMNTS
SEPTEMBER 17, 2020
In notes on its most recent (August) meeting of the bank’s Payments System Board, the members said that “at present there is not a strong public-policy case for issuance in Australia, given that the electronic payments system in Australia compares very favorably with those in many other countries and access to cash remains good.”.

Abrigo
MAY 27, 2022
In addition to having credit risk software, supportive policies and procedure, a credit manager at a financial institution requires well-honed skills. Often, having easy access to data through credit risk software can help complete the view of the risk landscape. Takeaway 3 Have integrity. Integrity leads to trust and that's important.

TheGuardian
NOVEMBER 25, 2023
Part of the discrepancy lies in the banks’ approach to arranging bonds, which are used by companies to access financing along with, and sometimes instead of, a direct loan.

PYMNTS
DECEMBER 21, 2020
Combined with a year unlike any other, we knew it was time to look at our return policies and processes to ensure they were safe and headache-free,” Linne Fulcher , vice president, customer strategy, science and journeys, Walmart U.S., said in the post.

PYMNTS
JANUARY 27, 2020
Fraudsters’ attempts to access systems and steal valuable information are becoming more innovative, and research suggests they are also increasingly successful. Companies can address these security gaps by updating policies to require clean desks and other specific expectations for remote workers. million in 2019 — a 1.5

PYMNTS
DECEMBER 27, 2020
a security firm, on Thursday said its unidentified software vendor had been comprised and hackers used the access try to read Crowdstrike’s internal email, Reuters reported. Reuters quoted an unidentified source as saying of the attack several months ago: “They got in through the reseller’s access and tried to enable mail ‘read’ privileges.
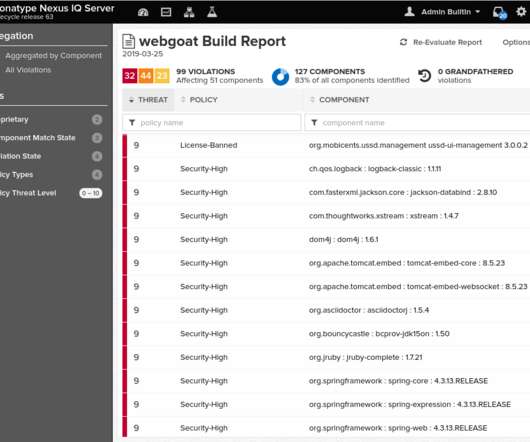
Perficient
JUNE 5, 2020
For the purpose of efficiency, these policies should be encoded into an automated scanning tool, with the output a set of recommended remediation steps to reduce or remove the detected vulnerabilities. The common approach is via segregating these secrets in a “vault” that is accessed during the Continuous Deployment process.

PYMNTS
APRIL 6, 2020
Rifkin Weiner Livingston LLC has filed an amended complaint against Bank of America (BoA) for allegedly giving its lending clients a higher priority and denying or limiting access to the Paycheck Protection Program (PPP) to its depository clients and other small firms, according to a press release.

PYMNTS
SEPTEMBER 22, 2020
Google and its employees are making policies which are over and above the laws of our country, and are arbitrarily implementing them.”. Google offered its own take on the situation, though without identifying Paytm specifically, in a post on its Google India blog titled “Understanding our Play gambling policies in India.”.

Perficient
OCTOBER 26, 2022
More accessible and digestible data gives organizations the information required to build the kind of intuitive, tailored products that customers want and need. Access to data gives companies the understanding they need to match such a product to an appropriate consumer. Implement rewards and loyalty programs.

PYMNTS
SEPTEMBER 23, 2020
United Airlines has launched an interactive map feature, Map Search , to let users access flight times, prices and other data, according to a company blog post. The feature, powered by Google 's Flight Search enterprise technology, can be accessed on the company's website.

PYMNTS
NOVEMBER 25, 2019
After using their accounts to log into specific Android apps downloaded from the Google Play store, Twitter and Facebook noted that the personal information of hundreds of users might have been accessed improperly. We encourage people to be cautious when choosing which third-party apps are granted access to their social media accounts.”.

Bank Innovation
AUGUST 15, 2017
This is because of Apple’s contactless policy, which allows access to only […]. Starting this week, people can tap their phones to pay and enter a station. iPhone users however, cannot enjoy this convenience.

BankUnderground
JUNE 1, 2023
Sangyup Choi, Tim Willems and Seung Yong Yoo How does monetary policy really affect the real economy? What kinds of firms or industries are more sensitive to changes in the stance of monetary policy, and through which exact channels? ’), which is why we are interested in creating a broad database of such shocks.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content